Threat Detection and Response
Network and Endpoint Threat Correlation
Hackers are designing malware to be more sophisticated than ever. Through packing, encryption, and polymorphism, cyber criminals are ready to disguise their attacks to avoid discovery. Zero-day threats and advanced malware fluently slip down antivirus results that are simply too slow to reply to the constant stream of emerging threats. Organizations of all sizes need an answer that leverages a holistic approach to security from the network to the endpoint. WatchGuard trouble Discovery and Response( TDR) is a powerful collection of advanced malware defense tools that correlate threat indicators from Firebox appliances and Host Sensors to prevent known, unknown, and evasive malware threats.
Key Features
Improves security against advanced malware attacks, including ransomware
Correlates network and endpoint insight for enterprise-grade threat visibility
Scores threat indicators and incidents supported severity to guide response
Tight integration with APT Blocker for advanced threat triage
Works alongside existing antivirus solutions with no impact on endpoint performance
Decreases time to detection and remediation through policy-based automation
Threat Correlation and Prioritization
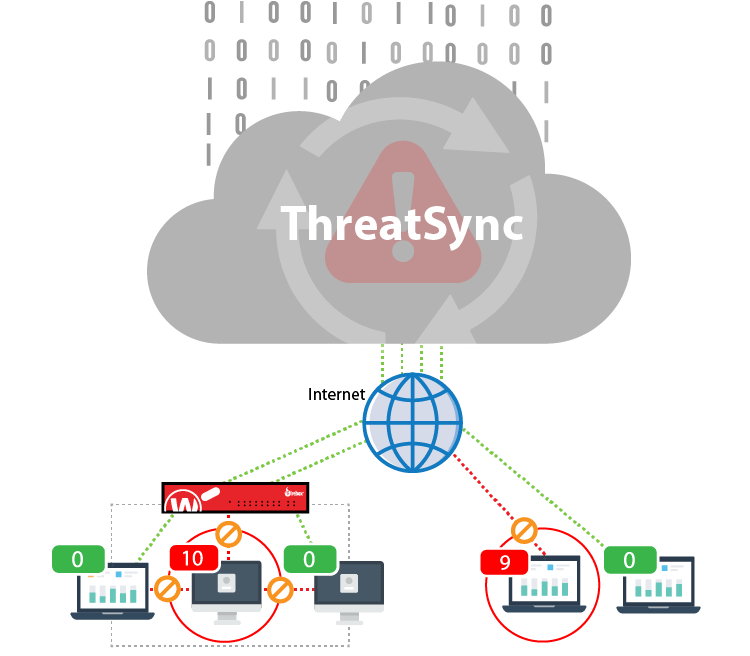
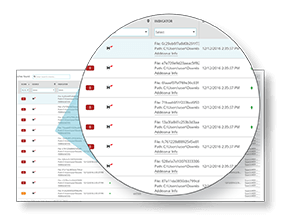
ThreatSync may be a Cloud-based correlation engine that analyzes event data from Host Sensors and Firebox appliances to identify malicious behavior. Threats are scored supported inflexibility, for guided remediation.
Threat Visibility on the Endpoint
The lightweight WatchGuard Host Sensor extends threat visibility and operation to the endpoint. The WatchGuard Host Sensor continuously sends heuristic and behavioral data from the endpoint up to ThreatSync for correlation and scoring.

Host Containment and Automated Response
Control infections automatically when a threat is identified. ThreatSync quickly contains any host machine from the network, preventing further infection of your business. Once contained, ThreatSync eliminates the malware by automatically killing processes, quarantining malicious files, and deleting associated registry keys.
Ransomware Prevention with HRP
Host Ransomware Prevention (HRP) may be a ransomware-specific module within TDR that uses behavioral analysis and honeypots to appear for signs of ransomware. If malware is detected, HRP automatically intervenes to prevent the ransomware before files are lost.

Advanced Threat Triage with APT Blocker
Want to need a deeper look at a suspicious file? Our integrated approach to threat triage uses an innovative artificial intelligence engine in conjunction with our APT Blocker Security Service, to detect and automatically send suspicious files for deep analysis during a coming-generation Cloud sandbox.
Learn MoreEmail Alerts & Notifications
ThreatSync includes email cautions and notifications to let you know when a threat indicator or incident has been detected, as well as if the threat has been remediated from the network or endpoint. announcements are configurable to ensure that you receive the alerts you want when you want them.

Enterprise-grade Threat Intelligence
Threat Intelligence was previously only a benefit available to enterprise organizations with big budgets and even bigger security teams. With Threat Detection and Response, WatchGuard aggregates and analyzes threat intelligence feeds – delivering safety benefits without passing on the associated complexities or cost.
Additional Security Layer to Existing Antivirus Solutions
Threat Detection and Response doesn’t require users or Managed Security Service Providers (MSSPs) to exchange existing AV solutions already deployed. TDR works in tandem with existing AV, bringing an extra, powerful layer of threat detection and event correlation to catch anything that AV might miss.
How It Works
Threats detected on the Firebox or via the Host Sensor are sent to ThreatSync, where they are continuously correlated and analyzed, then scored and ranked by severity. Threats can then be quickly remediated through one-click response options, or by leveraging policies to enable an automated response including quarantine the file, kill the process, and delete the registry key persistence.